DDoS Attack Mitigation on Heroku
Web-based SAAS applications are uniquely vulnerable to Distributed Denial of Service attacks.
First
Compared to attacks that exploit TCP flaws or other lower network level network responses the HTTP request/response cycle of web apps is much more expensive.
Second
Compared to other types of DDoS attacks, it can be much more of a challenge to filter out legitimate vs. illegitimate traffic. Consider an attack that uses a compromised browser extension to hammer a remote server: the requests would be virtually indistinguishable from user generated traffic.
What Users Will View
The image below is what will be shown to users who request a CAPTCHA protected URL on your Expedited WAF protected site.

Prerequisites
What you need to get started:
- Expedited WAF add-on is setup in front of your application.
How To Add CAPTCHAs to your Heroku App
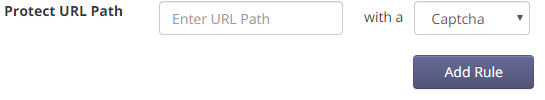
Add individual URLs to be presented with a CAPTCHA challenge from the Protected Pages screen of your Expedited WAF dashboard:
Notes
- CAPTCHA protection is optional. It is disabled by default and will only apply to the specific URLs that you include in a rule.
- Adding the root
/as a URL will CAPTCHA protect your entire site, but typically this isn’t needed.
Resources
Learn more about DDos Attacks