Safe ECC curves for HTTPS are coming sooner than you think
Making ECC better by simplifying it
Making ECC better by simplifying it
As we've mentioned, ECC certs are faster, stronger and better than the older RSA equivalents.
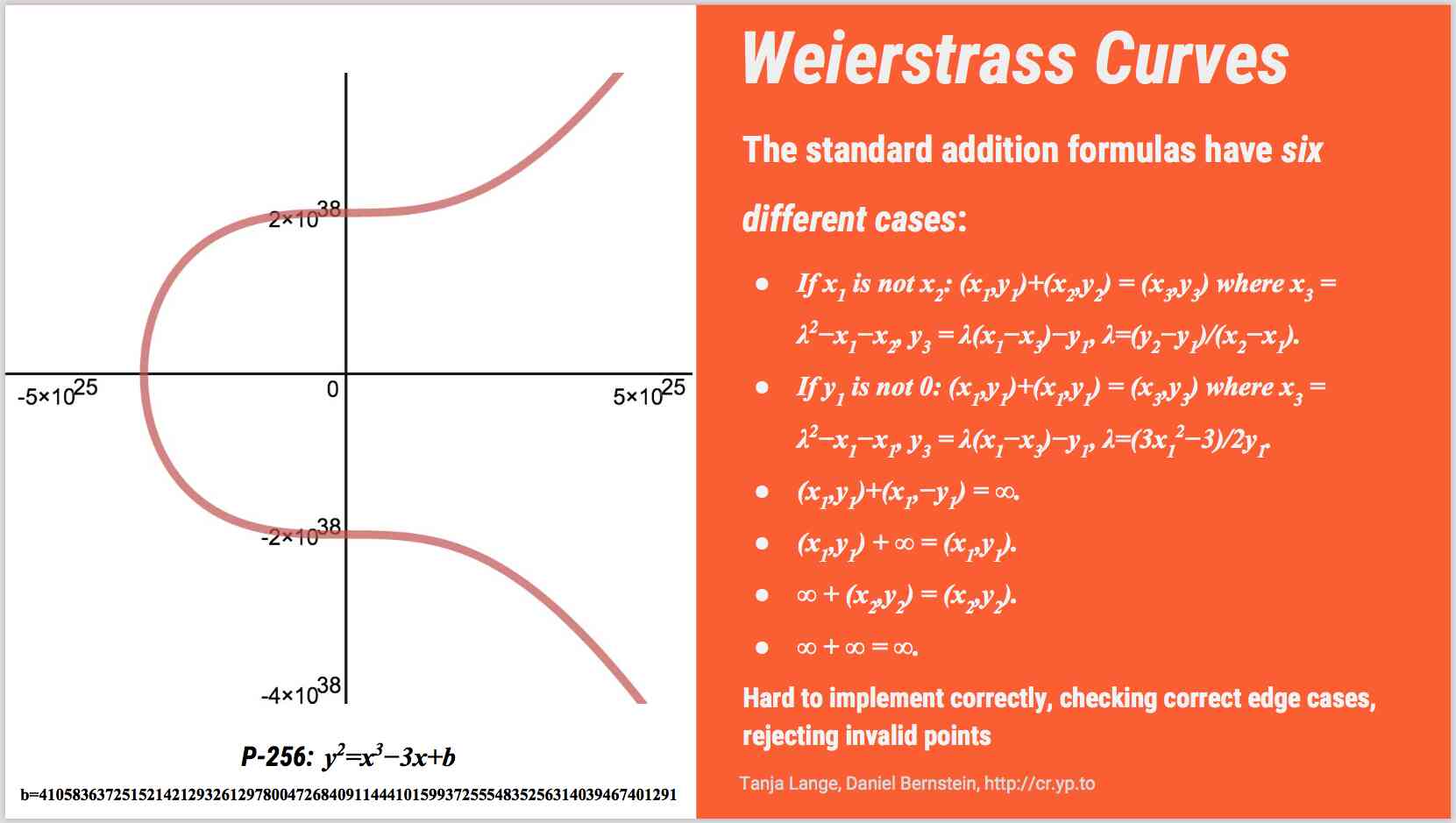
But picking a good curve can be difficult: there's concern that some of the popular curves have issues when weaker curve points are used in connections. Additionally, the maths for P256 has a lot of different cases: here's the standard Weierstrass curve you see in every 'introduction to elliptic curve cryptography' video, as well as the maths involved (thanks to Dierdre Connolly's excellent ECC talk for the images):
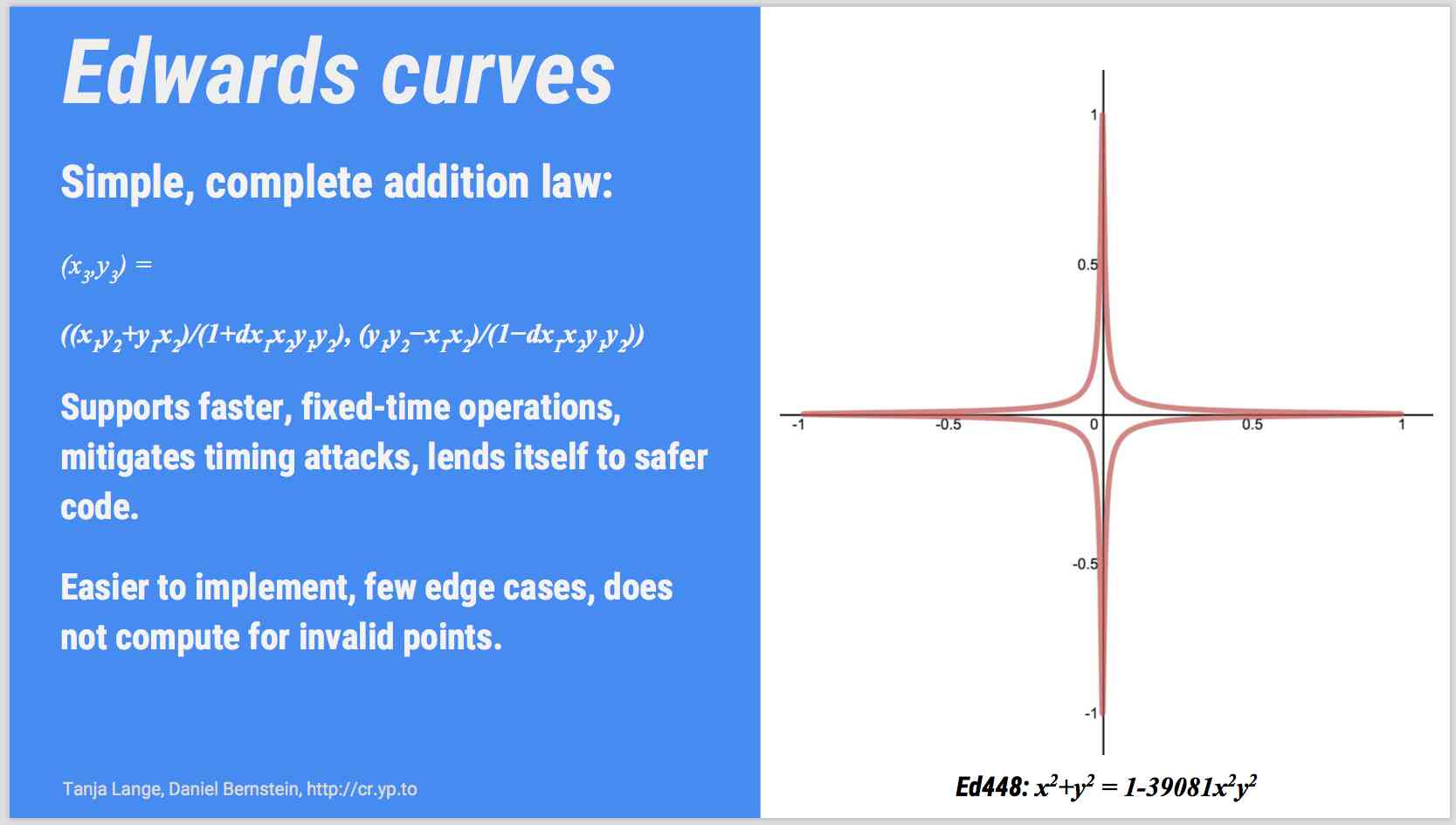
Here's an Edwards curve, like those used in Safecurves. The maths used to create Edwards curves is much, much simpler, meaning implementation flaws are easier to spot:
Software like Signal, WhatsApp, Viber and a bunch of other software already use Curve25519, one of the two curves on the IETF 'Elliptic Curves for Security' memo. I was wandering around OpenSSL 1.01 earlier today (infosec people wander around openssl a lot), and decided to check the curves available (type openssl ecparam -list_curves). Alas, none of the Safe Curves are in OpenSSL 1.0.
Apparently I'm not the only one who noticed.
Good news: OpenSSL 1.1 (currently in beta) has support for Curve 25519 - which is good, as it will probably included in the upcoming TLS 1.3 spec. I downloaded and built the OpenSSL 1.1 beta today, and ran:
openssl ecparam -list_curves
which returned a big list of supported curves including:
X25519 : X25519
X25519 is the function for the Curve25519 curve, one of the two safe curves recommended in RFC 7748. The other one, curve448, isn't in OpenSSL yet.
OpenSSL 1.1 is due any day now. Of course, you also need browser support:
No word on Firefox or Safari yet but with all the other pieces falling into place, we can probably expect them soon.
Simpler, safer ECC is on it's way soon!